The months of May and June have been marked by numerous cyber attacks is ransomware (type of malicious software created with the intention of blocking (encrypt) the access to files or systems and only release them after payment of a specified amount) and also other virtual pests are often not so well defined and that they have infected numerous computers around the world.
We're talking about the Wannacry/WannaCrypt/PetrWrap//SambaCry, Petya NotPetya, which caused serious problems and of course, it is common after this catastrophe Cybernetics, authorities and experts in information security fire an alert with measures to be implemented and followed by users and technology professionals.
It's been a real challenge for it professionals who manage daily Windows, Linux servers and workstations still running Windows, Linux or macOS (not to mention mobile devices) if anteverem and guard all virtual pests are circling the cyberspace in search of vulnerabilities in operating systems and other suites.
But lest all this environment can coexist, we need to have an interoperability between operating systems, and other protocols. It is exactly this scenario we will analyze the behavior of the Wannacry/WannaCrypt/PetrWrap//SambaCry and Petya NotPetya.
WannaCry: From changes in the Eternalblue code, this created by NSA and that after the Group Shadow Brokers, which exploits a vulnerability in Windows SMB Protocol on port 139 and 445, revealed it. The EternalBlue had as target Windows Server 2008 R2, Windows Server 2008, Windows XP, Windows Vista and Windows 7 (both x 86 platform as x 64).
Types of files it encrypts:
.doc .docx. docb .docm. dot .dotm .dotx .xls .xlsx. xlsm .xlsb .xlw .xlt .XLM .xlc .xltx .xltm .ppt, .pptx .pptm. pot .pps .ppsm .ppsx .ppam .potx .potm .ost .pst .eml .msg. edb .vsd. vsdx .txt .csv .RTF. 123. wks. wk1 .pdf. dwg. onetoc2. snt. hwp. 602. sxi. sti. sldx. sldm. sldm. vdi .VMDK. vmx. gpg. aes. ARC. PAQ. bz2. tbk. bak .tar .tgz .gz. 7z .rar .zip. backup .ISO. vcd .JPEG .jpg .PNG .gif .bmp raw .tif .TIFF .CGM. nef .PSD. Oh. svg. .DjVu m4u .m3u. mid. wma .FLV. 3 g 2. mkv .mov .mp4 .3gp .avi. .MPEG. asf vob. mpg. wmv .fla file .swf. wav .MP3 .sh .jar java .class. rb .php .jsp .ASP. brd. sch. dch. dip pl. vb. vbs .ps1 .bat .cmd. js. asm. pas. cpp c. cs. suo .sln .ldf. ibd. myi. myd. frm. ODB. dbf. db .mdb .accdb. sql. sqlitedb. sqlite3. asc. lay6. lay. mml. sxm. otg. odg. uop. STD. sxd. otp .ODP. wb2. slk. diff. stc .SXC. ots .ODS. 3 DM. max .3ds. uot. stw .sxw. ott .ODT .PEM .p12. csr .CRT. key .pfx. der
Petya/PetrWrap/NotPetya: According to analysis, the Petya the exploit code EternalBlue and also the EternalRomance, uses a remote code exploitation via TCP port 139 and 445 in addition to using PsExec (Sysinternals Windows administration tool that allows you to run commands on remote systems on other systems, with full interactivity and without having to manually install software) and WMI (enables management of network devices and applications from Windows computing systems). Microsoft also confirmed that the first systems were infected through the automatic update mechanism of a Ukrainian third-party software product called M.E. Doc.
The Petya acts when he allowed he administrator encrypts the entire disk and overwrites the Master Boot Record (MBR) and on the other hand, if you do not have administrator privileges, it just starts to encrypt the file types specified:
.3ds .7z .accdb. ai .ASP .aspx. avhd. back .bak. c. cfg file .cpp, .cs. ctl .dbf. disk. djvu .doc .docx .DWG .eml. fdb .gz. hdd. e-mail kdbx. mdb .msg .NRG. well. ost. ova. ovf .pdf. php. pmf .ppt, .pptx. pst. pvi. py. pyc .rar .RTF .sln. sql. tar. vbox .vbs. vcb. vdi. vfd .VMDK .vmc. vmsd. vmx. vsdx. vsv. work .xls .xlsx. xvd .zip
The mode of operation of Petya leads to believe that the attack does not seem to just want to raise money, but rather, that if successful in this otvivesse implementation, is not to find an operating system where the user had required privileges he then leaves for the destruction of the data, in the case of part of the Master Boot Record (MBR).
The machines that were corrected against following the bulletin MS17 holdings-010 or deactivated SMBv1 as kb2696547 were not affected.
Linux/Samba
While the Windows operating system was the target of WannaCry, Linux with Samba installed was exploited by SambaCry, with the same vulnerability in the server message block (SMB) Protocol. Samba is an open source project which I had your first version written at the beginning of 1992 is widely used in Linux and Unix computers so that they can work with files and Windows print services. With him we have a Linux client that can connect to Windows servers or have a Linux server that allows connections from Windows clients. In some scenarios you can still use the Samba as an LDAP server (similar to Active Directory in Windows) and thus authenticating and controlling access to a Windows/Linux network.
SambaCry: Called SambaCry by your resemblance to WannaCry as it tries to exploit the vulnerability of the SMB protocol targeting find a network share that has credentials with read/write permission on a share where then attempts to copy a Linux library that was created with malicious code. Samba through the CVE-2017-7494 reported that "all versions of Samba 3.5.0 from onwards are vulnerable to a remote"
Our environment
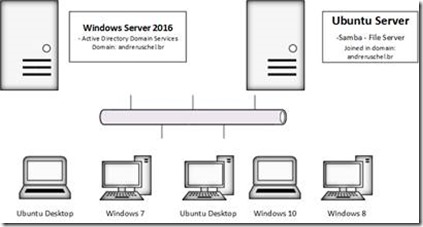
We envision a scenario that consists of a server running Windows Server 2016 having the function of Active Directory, a Linux server with Ubuntu Server having the installed Samba (file server) and workstations with Windows 10, Windows 8, 8.1, Windows 7 and Ubuntu Desktop 17.04 all Member of the Windows domain (andreruschel.br).
Figure 1. Small sketch of the environment
Ubuntu Server-Samba in Windows Server Active Directory 2016
So that we can manage permissions to access the directories it is necessary that the server on Linux (Ubuntu Server) is a member of the Active Directory domain Dicrectory.
Access the terminal as root and edit the/etc/hosts file by adding the following content:
server2016 server2016.andreruschel.br 192.168.1.100
Where:
Server IP: 192.168.1.100
Hostname: server2016
Domain: andreruschel.br
Edit the/etc/resolv.conf file adding the following content:
nameserver 192.168.1.100
Search andreruschel.br
Where:
Windows Server IP: 192.168.1.100
Kerberos:
To install the packages on Linux station, open the terminal as root and type:
aptitude install krb5-user libpam-krb5 krb5-config libkrb53 libkadm55
Edit the/etc/krb5.conf file adding the following content:
[libdefaults]
default_realm = ANDRERUSCHEL.BR
dns_lookup_realm = true
dns_lookup_kdc = true
ticket_lifetime = 12:00 am
Forwardable = yes
[realms]
ANDRERUSCHEL.BR = {
KDC = server2016.andreruschel.br
admin_server = server2016.andreruschel.br
default_domain = ANDRERUSCHEL.BR
}
[domain_realm]
. andreruschel.br = ANDRERUSCHEL.BR
andreruschel.br = ANDRERUSCHEL.BR
Samba and Winbind:
Install the needed packages:
apt-get install samba winbind smbclient samba-common smbfs
Edit the/etc/samba/smb.conf file by adding the following content:
Note that in:
securiy use ads
realm use andreruschel.br
Workgroup = andreruschel
Max log size = 50
Security = ads
password server = server2016.andreruschel.br
realm = ANDRERUSCHEL.BR
idmap uid = 1000-2000000
idmap gid = 1000-2000000
template shell =/bin/bash
template homedir =/home/%U
winbind use default domain = true
winbind enum users = yes
winbind enum groups = yes
winbind separator = +
winbind refresh tickets = yes
winbind nested groups = yes
Edit the/etc/nsswitch.conf file adding the following content where we must inform where it must get login information once, we have users and groups, let's use the following configuration:
passwd: compat winbind
Group: compat winbind
shadow: compat
Configuring PAM
Edit/etc/pam.d/common-auth adding the following content:
auth sufficient pam_unix.so
pam_winbind.so use_first_pass auth required
auth required pam_deny.so
Edit/etc/pam.d/common-session adding the following content:
session required pam_permit.so
session optional pam_winbind.so
session required pam_unix.so
session optional/etc/skel/skel = pam_mkhomedir.so umask 0077
session optional pam_mount.so
Edit/etc/pam.d/common-account by adding the following content:
account sufficient pam_unix.so
account required pam_winbind.so use_first_pass
Restarting the Winbind
/etc/init.d/winbind restart
Testing the Kerberos
We will then test the Kerberos authentication using the user Administrator.
On the Linux server, open the terminal as root and type:
$ sudo Kinit administrator@ANDRERUSCHEL.BR
If you have everything right we have the following result:
Using short domain name--ANDRERUSCHEL
Joined ' FSLINUX ' to ' andreruschel.br ' realm
Still in terminal of the Linux server, as root, we will get a ticket by entering the command klist:
$ sudo Klist
Ticket cache: FILE:/tmp/krb5cc_1000
Default: Administrator@ANDRERUSCHEL.BR
Valid starting Expires Service principal
krbtgt/04/07/17 15:34:06 04/10/18 01:34:09 ANDRERUSCHEL. BR@ANDRERUSCHEL.BR
renew until 04/07/17 15:34:06
Ticket obtained with success!
Joining Linux server in Active Directory
Carried out the initial steps, we will illustrate how to join the Ubuntu Server andreruschel.br Windows Server domain. In the terminal of the Linux server, type:
sudo net ads join-U Administrator
Enter the password for the user Administrator (Windows domain)
To verify winbind can see Active Directory users run the command:
$ sudo wbinfo-u
You should obtain the following result where Active Directory users will be listed:
fslinux\andreruschel
fslinux\anaruschel
fslinux\alexandre
fslinux\eduardo
fslinux\giovana
fslinux\viviani
Guest
Administrator
With your Ubuntu Server member of the Active Directory domain in Windows Server 2016 you can still configure the SeDiskOperatorPrivilege on your Linux server to manage that can manage share permissions directly on the Server Windows Server.
When we have a file server which is a Linux server with Samba installed, you shall function to share directories for Linux and Windows workstations can then access the files on that server. That's exactly where even though you have the Linux server with Samba updated (version 4.6.5) containing shares files that will be consumed by Windows stations shall be vulnerable if the Windows station will be infected by the Wannacry/WannaCrypt. I'm referring to the files shared by the Linux server which are documents with extensions targeted virtual pests, but it cited on the other hand, the Linux server itself, this will not be compromised by the SMB vulnerability due to be with Samba properly updated.
Upgrading Samba
Before you perform this procedure is ideal that you perform the backup of smb.conf file.
Ubuntu Server
Check for new packages available and update the samba package as follows:
$ sudo apt-get update
$ sudo apt-get dist-upgrade
Check which version of Samba that is running:
smbstatus --version
Before you update the Samba, it is necessary to ensure that all dependencies are installed.
For this run:
apt-get install acl attr autoconf build-essential bison \
Debhelper dnsutils xml docbook-xsl docbook-flex gdb krb5-user \
Libacl1-dev libaio-dev libattr1-dev libblkid-dev libbsd-dev \
Libcups2-dev libcap-dev libgnutls-dev libjson-perl \
Libldap2-dev libncurses5-dev libpam0g-dev libparse-yapp-perl \
Libpopt-dev libreadline-dev perl perl-modules pkg-config \
Python-all-dev python-dev python-dnspython python-crypto \
Xsltproc libgpgme11-dev zlib1g-dev python-gpgme python-m2crypto
Now let's stop the Samba service:
/etc/init.d/samba stop
Downloading and extracting the source files:
wget https://www.samba.org/samba/ftp/samba-latest.tar.gz
tar xzf samba-latest.tar.gz
cd samba-4.6.5
Run:
./configure
make
make install
Restart the service:
/etc/init.d/samba restart
And check if you are already running the updated version:
smbstatus --version
Should return the Samba version 4.6.5
With that you correct the CVE-Samba 2017-7494.
Petya destroys only MBR (Master Boot Record) of hard disk (Disk1)
This test is one of our favorites, where our computer became infected with Petya, which possessed Windows 7 containing two hard drives:
Figure 2. Example of a computer with two hard drives with Petya
Result: The hard drive containing the operating system had your MBR (Master Boot Record) partially destroyed, however the second hard drive had no damage on your MBR (Master Boot Record) or even data has been compromised.
Protecting your data or backup built into Windows and Linux
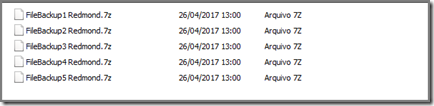
In our test lab we conduct the procedure of renaming the backup files that have the extensions targets and had some good results:
1- You perform backups on external and internal disk or even to your backup tool generates files with known extensions, which we cite are targets of these variants;
2- Assuming that your backups are on another hard drive and have the extensions 7z, zip, rar or SQL;
3- Include the following script after the execution of our backup tool to rename multiple files at once:
Linux (renaming all files 7z extension directory to. @andreruschel)
Rename's/\ .7z $/@andreruschel/\. ' * .7z
Windows
forfiles/P e:\backup\/c "cmd/c @path rename @fname. @andreruschel"
Where:
e:\backup-where are the backup files
. @andreruschel – extension to be given to the archives
Result: Note that we rename all files to .@andreruschel before infecting with Wannacry/SambaCry and PetrWrap/NotPetya/Piotr:
Figure 3. Renamed files before the Wannacry/WannaCrypt
After infection with Wannacry/WannaCrypt/SambaCry/PetrWrap/NotPetya Petya and the files were not encrypted because the . @andreruschel extension is not part of the extensions targets.
Once this is done, simply remove the hard drive and put in another computer and run the following script to rename all the files to 7z again:
Windows
forfiles/P e:\backup\/c "cmd/c @path rename @fname .7z"
Figure 4. Renamed files after Wannacry/WannaCrypt
Result: After the process cited all files were intact.
Final analysis and new challenges
In our analysis we take into consideration a mixed environment and interoperable, but regardless of whether you have a Windows or Linux only environment, you should always keep your operating systems and other suites or applications properly updated.
All virtual pests cited operating in one way or another systems vulnerabilities in that administrators do not have the proper security updates. We believe that these problems will not stop here and without a doubt it is essential we are constantly planning for the next attack will come.
Study links:
bit.ly/ruschelms17010
bit.ly/ruschelsmb
bit.ly/ruschelwannacrypt
bit.ly/ruschelpetya
bit.ly/ruschelcifs
André Ruschel is researcher, IT speaker, Forensic computer scientist, entrepreneur, author several books, MVP Cloud and Datacenter Management, specialist in interoperability and inventor of ThinEco Cardboard Computer.






Nenhum comentário:
Postar um comentário